China's National Computer Virus Emergency Response Center on Monday released its latest report on Volt Typhoon, once again exposing cyber espionage and disinformation operations conducted by US government agencies, including a US cyber weapon that can mislead investigation and frame other countries for its own cyber espionage activities.
China's National Computer Virus Emergency Response Center on Monday released its latest report on Volt Typhoon, once again exposing cyber espionage and disinformation operations conducted by US government agencies, including a US cyber weapon that can mislead investigation and frame other countries for its own cyber espionage activities. This is also the first time for the center to release the report in multiple languages, including Chinese, English, French, German and Japanese.
The Monday report is the third report on Volt Typhoon released by National Computer Virus Emergency Response Center and National Engineering Laboratory for Computer Virus Prevention Technology. It further disclosed the cyber espionage operations targeting China, Germany and other countries which were launched by the US and other Five Eyes countries.
On May 24, 2023, the cybersecurity authorities from The Five Eyes countries, the US, the UK, Australia, Canada and New Zealand, issued a joint cybersecurity advisory, claiming that they had discovered cluster of activity of interest associated with a "China state-sponsored cyber actor," known as Volt Typhoon, and these activities "affected networks across US critical infrastructure sectors."
On April 15 and July 8, the National Computer Virus Emergency Response Center, National Engineering Laboratory for Computer Virus Prevention Technology and 360 Digital Security Group jointly released two investigation reports disclosing the US government's narrative regarding Volt Typhoon is purely a fabrication crafted by the US. The two reports also expose how US government agencies, in order to maintain control over the so-called "warrantless surveillance rights," conduct indiscriminate monitoring of global telecommunications and internet users. This is done to enable related interest groups to gain greater political and economic benefits by fabricating nonexistent Chinese cyberattack threats. The nature of the event resembles a "house of cards" conspiratorial swindling campaign scheme targeting the US Congress and taxpayers.
"After we released the reports in April and July on Volt Typhoon, more than 50 cyber security experts from US, Europe, Asia and other countries and regions have contacted us through various ways. They believed that the US government and Microsoft have attributed Volt Typhoon to Chinese government without any concrete evidence, and they also expressed concern about the US government's fabrication of Volt Typhoon," a research fellow from the National Computer Virus Emergency Response Center told the Global Times on Monday.
Secret weapons
The US is the world's largest arms dealer and its cyber weapon arsenal is not only large in scale, but also sophisticated in function. Previously, the National Computer Virus Emergency Response Center publicly disclosed multiple types of cyber weapons which were developed by the National Security Agency (NSA) and Central Intelligence Agency (CIA).
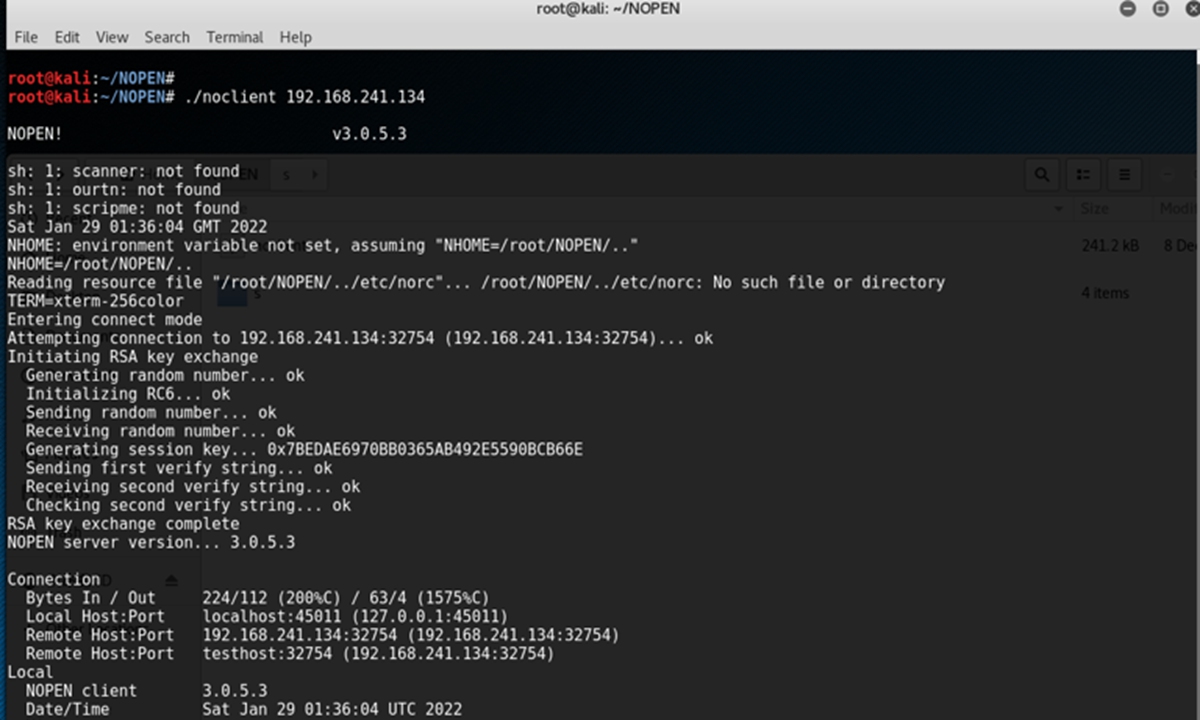
The Monday report unveiled information on a customized stealth "toolkit" codenamed "Marble" that the US agencies have developed to cover up their Computer Network Exploitation (CNE) operations, mislead attribution analysis and shift the blame on other countries.
The toolkit is a framework that can be integrated with other cyber weapon development projects, assisting developers to obfuscate various identifiable strings in program code, effectively "erasing" the "fingerprints" of cyber weapon developers, according to the report.
For a long time, the US has kept pushing a "Defend Forward" strategy in cyberspace, and implement the "Hunt Forward" operations, which means to deploy cyber-war forces in the surrounding areas of adversary countries to conduct close-in reconnaissance and network penetration. In order to satisfy those tactical needs, the toolkit "Marble" was developed, said the anonymous researcher.
The framework also has a "dirty" feature, which is the ability to insert strings in other languages at will, such as Chinese, Russian, Korean, Persian, and Arabic. This is intended to mislead investigators and defame China, Russia, North Korea, Iran, and Arab countries, said the researcher.
By tracing and analyzing the source code and comments of "Marble" framework, researchers also found that it has been identified as a secret weapon development program, which is not allowed to share with any foreign country, starting no later than 2015. This secret weapon was tailored by US intelligence agencies for themselves, and was even kept a secret from the so-called ally countries.
Recent findings in the report have once again highlighted who poses the greatest threat to global cyberspace security. The US government not only disregards the report but also continues to disseminate false information about Volt Typhoon, said Chinese Foreign Ministry spokesperson Mao Ning on Monday. China condemns US' irresponsible actions and urges it to immediately cease its global cyberattacks and stop using cybersecurity issues to slander and malign China, Mao said.
'False flag' operation
A "False Flag" is a deceptive act or operation carried out to make it appear as if it was conducted by another party. According to the report, the "Marble" framework fully exposes the indiscriminate and bottomless cyber espionage activities around the world carried out by US intelligence agencies, and their conspiracy to mislead investigators and researchers through "false flag" operations, so that to frame "adversary countries."
The anonymous researcher said that in conjunction with previous investigation findings, the hackers from US cyber forces and intelligence agencies disguise themselves like chameleons in cyberspace, pretend to come from other countries to carry out cyberattacks and espionage activities around the world, and pouring dirty water on non-ally countries of the US.
The report also noted that the "False Flag" operation is actually an important component of the US intelligence agency's "EFFECTS Operation," known as the "Online Covert Action" in the UK. The secret documents from the US and Five Eyes Alliance show that, the "EFFECTS Operation" includes two broad categories, "Information Operations" and "Technical Disruption Operations."
The Internal documents of the US and Five Eyes Alliance clearly indicate that the implementation of this "EFFECTS Operation" must adhere to four main principles, which are "Deny," "Disrupt," "Degrade," "Deceive." And these four main principles precisely cover all the core elements of the Volt Typhoon operation, said the report.
Subsea cable tapping sites
According the top secret files of NSA, the US has been controlling the world's most important internet "choke points," such as the Atlantic and Pacific subsea cables, constructing at least seven full-traffic tapping sites. All these sites are operated by NSA, FBI and NCSC from UK. Each packet through the sites is being intercepted and deeply inspected indiscriminately, according to the report.
The US National Security Agency is not content with merely focusing on the specific areas covered by submarine cables, and the data intercepted by these surveillance systems falls far short of meeting its intelligence needs. Therefore, the US has conducted CNE operations on specific targets located in the "blind spots" of its surveillance systems.
Top secret documents from the NSA show that the Office of Tailored Access Operation (TAO) of NSA has launched massive CNE operations around the world and implanted more than 50,000 spyware implants. Victims are mainly concentrated in Asia, Eastern Europe, Africa, the Middle East and South America. The internal documents of the NSA showed that almost all major cities in China are within the scope of NSA's operations, a large number of entities and their network assets have been compromised, said the report.
Spying on 'allies'
The report also cites instances of the US conducting surveillance on countries such as France, Germany, and Japan.
The anonymous researcher said US intelligence agencies have established a large-scale global Internet surveillance network, providing a large amount of high-value intelligence to the US government agencies, which offers the US government great advantage in the diplomatic, military, economic, scientific and technological fields. The US government and its intelligence agencies could put anyone on the "list" of monitoring.
For example, from 2004 to 2012, the US carried out a long-term espionage operation against France, monitoring the movements of the French government on policy, diplomacy, finance, international exchanges, infrastructure construction, business and trade. Some important intelligence was authorized by the US to be shared with the other "Five Eyes" countries. This shows that the countries of the "Five Eyes" alliance are also beneficiaries of US espionage operations.
A 'snooper' in cyberspace
The report said that the US global Internet surveillance programs and stations are like ubiquitous "snoopers" in cyberspace and steal user data from the global internet in real time, and this eavesdropping capability has become an indispensable foundation of the US efforts to build the "Empire of Hacking" and the "Empire of Surveillance."
To maintain such a huge surveillance program, the annual funding budget is quite huge, and with the explosive growth of internet data, the demand for funding is bound to "rise." This is also one of the main reasons why the US government conspired with its intelligence agencies to plan and promote the Volt Typhoon operation, said the report.
Over the years, the US government has kept politicizing the issue of cyberattack attribution in a way that serves its own self-interests. Some companies, such as Microsoft and CrowdStrike, have been influenced by the desire to appeal to US politicians, government agencies and intelligence agencies, as well as to enhance commercial interests. They kept using a variety of names with geo-political features to describe the hacking groups in the absence of sufficient evidence and rigorous technical analyses, such as "Typhoon," "Panda" and "Dragon."
In its last part, the report said that the international communications in cybersecurity industry is vital as the geopolitical landscape is growing increasingly complex and cybersecurity requires extensive international collaboration.
"We look forward to seeing that all cybersecurity firms and research institutes will keep focusing on the research of cybersecurity threat prevention technology and how to provide users with higher-quality products and services, which will then keep the internet developing in a healthy way along with the progress of human society," said the report.
https://www.cverc.org.cn/head/zhaiyao/futetaifeng3_CN.pdf
https://www.cverc.org.cn/head/zhaiyao/futetaifeng3_EN.pdf
https://www.cverc.org.cn/head/zhaiyao/futetaifeng3_FR.pdf
https://www.cverc.org.cn/head/zhaiyao/futetaifeng3_JP.pdf
https://www.cverc.org.cn/head/zhaiyao/futetaifeng3_DE.pdfSource link




 Cybersecurity. Photo: VCG
Cybersecurity. Photo: VCG